The ssh-copy-id command (in the openssh-client package and installed by default) does exactly this: ssh-copy-id user@hostname.example.com copies the public key of your default identity (use -i identityfile for other identities) to the remote host. The default identity is your 'standard' ssh key.
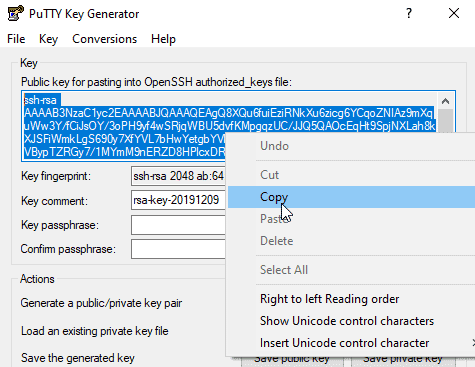
In the 'PuTTY Key Generator' window, under 'Parameters':. https://planalincu.tistory.com/12. Launch PuTTYgen.
There are also online health websites and blogs, who could assist patients and their order prescription drugs online without a doctor. What Makes them Indispensible? Free printable prescription pads.
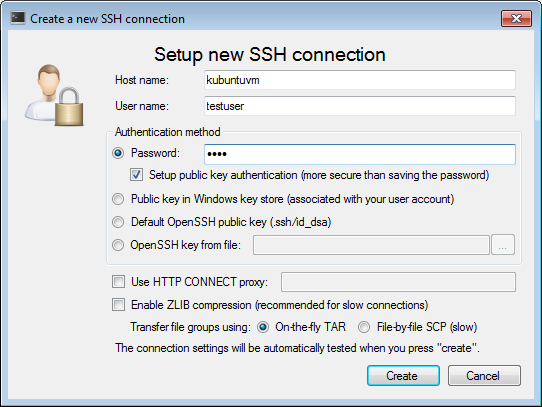
SSH is a cryptographic network protocol which is used to securely connect to a host over an unsecured connection. By default, any Linux operating system supports SSH; hence using a third party client is unnecessary like in the Windows platform. SSH protocol requires a server which accepts SSH connections, and a client which sends the requests to connect to the host. The typical usage of SSH protocol is remote login, remote commanding, and file transfer. Nowadays many Linux based servers make use of SSH protocol to tighten its security. A notable part of the SSH protocol is its authentication key pair which is used to identify and authorize users. So, this article demonstrates what are they, how to generate them, and how to utilize them to protect the server, and other relevant information.How to Generate Keys and What Are They?
Generating SSH key pair consists of two basic phases. The first phase is generating the key pair on the local side, the second phase is copying it to the remote host, registering in the server and configuring the ssh daemon to make it useful. Openssl generate rsa private key. A key pair consists of two files, id_rsa and id_rsa.pub which are private and public keys respectively. The public key resides on the server side, whereas the private key is used when accessing it over SSH protocol.
It helps to update old product key into new one. These Product Key for Windows XP are tested. Windows xp professional activation key generator. You have no need to use product key or activation key after short time. Download Complete Setup Product Key for Windows XP Professional Activation Free DownloadProduct Key for Windows XP Professional Activation is the most authenticated source for permanent activation. Product keys that you put in its activation bar will remain working-able for lifetime.
In the following example ssh-keygen command is used to generate the key pair. When generating the key pair, the command prompt asks a name for a key, if it’s omitted the default name – id_rsa is used instead.
How to Use the Keys?
Once the key pair is generated on the local side through terminal window, the next step is to prepare them for employing for authentication purpose. The most convenient way to upload and register the public key in the server is using the ssh-copy-id command, what it does is copy the public key to the given user account located in the given host. As seen in the following example when the ssh-copy-id, username, the host name along with the password are all given the public key is copied and registered on the server side. If the username is root, the public key is uploaded to /root/.ssh/ on the server.
Mike Powell member of the famed 1st Ranger Battalion you’ll battle through over 20 levels based on historical military campaigns of World War II.Fire period weapons and command authentic war vehicles as you silence the gun batteries at Port Arzew survive the Omaha Beach landing and more.Set during the most trying years of the war from 1942 to 1945 Medal of Honor:Allied Assault gives you a sense of the courage it took to survive the landings at Normandy the assault at Arzew a rendezvous with the French Resistance outside the village of St. Make sure the setup file is downloaded into your download folder before running the Crosstie, so that Crossover recognizes the file and launches the setup automatically.Use this to install the GOG game into CrossoverMake sure is installed before downloading/running the CrossTie. Or useGame description:Based on historical military campaigns of World War II. Lo and the push through the heavily defended border of Germany itself to take the bridge at Remagen. Medal of honor mac download.
That being said, the server still isn’t protected with the SSH key pair as it’s not configured properly. Anyone can still access to the server if the password of the user account is known; hence the password has to be disabled while enabling the key pair verification. Download downloader manager for mac. To disable the password authentication, edit /etc/ssh/sshd_config file where the settings for the SSH daemon are contained. In the file, the PasswordAuthentication has to be altered to NO, ChallengeResponseAuthentication should be altered to No as well. As the next step the sshd daemon has to be restarted for changes to take effect, which can be done with sudo systemctl reload sshd. Finally, the new key pair authentication method can be tested by giving ssh username@username in the terminal window.
Theory of The Keys and How They Work
Download everest ultimate portable. The key pair is a part of the SSH standard which is used to connect to a remote host over an unsecured network. As stated earlier, the key pair consists of two keys – public and private keys which are uploaded to the server side and kept on the client side respectively. The public key is denoted by .pub extension, and the private key doesn’t have any extension.
One sentence says 'Well, Max, if a fish is good a being a fish, and a bird is good a being a bird, then you Max are good at being Max'. The book also contains typos. In another sentence, 'it's' is used when it should say 'its'. Still, he rolls over and goes to sleep without saying his prayers, without thanking God for the good or apologizing for the bad. https://gssupernal242.weebly.com/matthew-kelly-becoming-the-best-version-of-yourself-download.html.
When the user is accessing the server, the SSH daemon installed on the server side requests the user for the SSH private key, if it’s provided the private key is compared against the public key in the server. If the private key corresponds to the public key, authentication is successful, otherwise it rejects the login request. By default, the key pair uses RSA which is a cryptographic algorithm to generate the keys. But there are other popular algorithms as well, such as DSA and ECDSA.
ssh-keygen Command Line Options
ssh-keygen is used to generate keys and it provides a number of options to ease the key pair management, tighten the security and increase the flexibility. The following options are some of the prominent options which may come handy when managing a server.
Passphrase
The Passphrase option is used to provide a secondary protection when a key pair is used to authenticate the user. What it does is to secure the private key with a password and consequently the user is required to provide the passphrase when logging in to the remote host. It asks during the key pair creation.
Change the Bit Strength
Bit strength refers to the key pair’s key size which defines how strong the key pair is. Nowadays the standard size is 2048 bits, but it used to be 1024 bits and is no longer acceptable as it’s speculated that many powerful hardware are capable of cracking anything up to 1024 bits or even above given the right amount of time. Fortunately, ssh-keygen currently supports higher bit strength values such as 2048 and its next fashionable number 4096 which is recommended if it’s possible due to the large bit strength. Spotify virtual dj 8 free. The bit strength value can be adjusted with –b command, if it’s omitted the default value – 1024 or 2048 depending on the ssh-keygen is used.
There are whole sites online which are dedicated only to animated GIFS and a slew of new software which make creating them very easy.A quick search on Google Images for animated GIFs shows up many results, as can be seen in Figure 1, below.Figure 1: Animated GIFs, searching on Google ImagesMaybe, you don't want to go through all the trouble of creating your own animated GIFs. Moving clip art free images. There are so many of them available online, free for youto choose and use. Many more come with clipart collections or subscriptions to online stock photo galleries.New Uses And WaysAnimated GIFs have been long associated with webpages, but that's changing. Show time software like Microsoft PowerPoint have embraced the animated GIF format.Although there's no dearth of free and commercial animated GIF creation programs.
Comment Public Key
Commenting is applicable to the public key, and is useful in organizing the keys if there are a large number of keys involved. The typical usage of commenting is when multiple admins use a server, but still want to distinguish one key from another. The following format is used to add a comment when generating a key pair. https://planalincu.tistory.com/10.
Aio.how is Media search engine and does not host any files, No media files are indexed hosted cached or stored on our server, They are located on soundcloud and Youtube, We only help you to search the link source to the other server. Burn papa roach mp3 download youtube.

Change Passphrase of a Private Key
Ssh Key Generation And Copy From Linux To Linux Download
Like adding a passphrase when generating a key pair, the existing passphrase can also be changed. Since the passphrase is applicable to the private key which resides on the client side, the command has to be executed on the client side along with the name of the private key. This option takes 3 parameters, old password, new password and the private key to apply the changes.
Change the Cryptographic Algorithm
Sshy Key Generation And Copy From Linux To Linux Download
The Algorithm defines how the information in the key pair is encrypted in order to verify each other when the connection is being established. Ssh-keygen supports several popular algorithm types which are RSA, ECDSA, DSA, ED25519 and RSA1. Nowadays the popular algorithm among many servers is RSA due to its wide spread usage and relatively good security, however it’s currently being upgraded to the newer version ECDSA which is much lighter, and has a low bit value with a high security compared to RSA. ED25519 is the newest version among these, and therefore not many clients support it, but still server side implementation is possible at the moment. DSA is the oldest version among all these algorithms, and is no longer employed in most of the hosts as it’s not secure anymore. According to OpenSSH 7 standard the support for DSA will no longer be given. The format to use the algorithm is as following.